The needs of the next generation are increasing on a daily basis. Whether it is about finance, artistic requirements, or any other necessities, technology also plays a vital role.
How can one forget blockchain security if the aspects of technology are discussed in groups or big promotional events?
It can actively let business individuals and professionals – statistical experts, CPAs, and individuals well-versed with trends of payroll administration – securely use their cash electronically in different cloud computing environments.
One must not deny the fact that the security involving hybrid cloud benefits and other types of computing is somewhere shaping the future.
Blockchain security solving real-time complexities in a computational manner
Rather than storing information onto a centralized database, it is better to keep the data safe via blockchain security that requires a distributed database for communication across peers without inviting third parties.
Moreover, the pillars of blockchain are so powerful that all the virtual transactions you process are recorded as per the standards of encryption.
You might be curious to know about the solutions offered by this multi-purpose technology that has been able to solve real-time problems in a much convenient manner. Let’s discuss them.
-
Fifty-one (51) percent [%] attack
One can pronounce fifty-one (51) percent [%] attack as a majority attack. It is one of the potential attacks ever happened on any of the existing blockchain networks. The majority of the hash rate has been controlled either by an organization or an entity that led to unwanted disruption over the network channels.
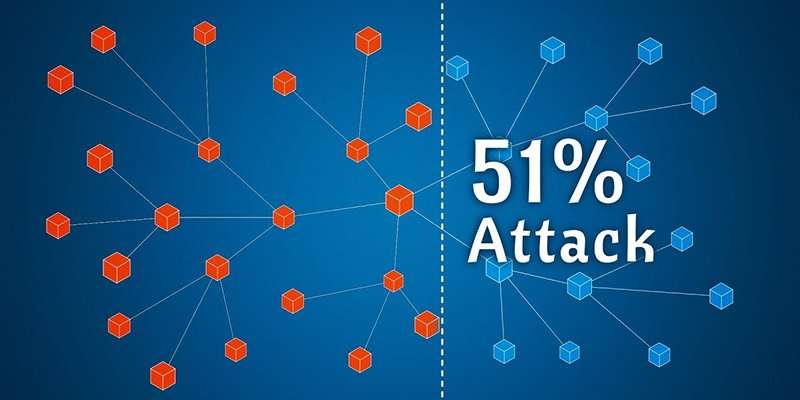
In such a scenario, the attacker would have a rough mining power to intentionally exclude or modify the ordering of transactions. They could also reverse the transactions they made when being in control leading to a double-spending problem.
A successful majority attack could also allow the attacker to prevent some or all transactions from being confirmed or to prevent miners from mining resulting in what is known as mining monopoly?
On the other hand, a majority attack won’t allow the attacker to revert transactions from other users – not to prevent transactions from being created and broadcasted to the network.
Changing the block’s reward, creating coins out of denial, or stealing coins that never belong to the attacker is also not possible.
Several miners have joined the blockchain network to contribute to its strength and security. If the miners are not acting honestly and strive to receive the block reward then the 51 percent attack is unlikely to occur due to the magnitude of the network.
After the blockchain grows in an uncontrollable manner, it is much obvious that a person or a group of users may not be overwhelming the participants with their choice of acquiring computing power of high-levels.
Also changing previously confirmed blocks gets more and more difficult when the chain grows because the blocks are linked and it is only possible to change a certain block if all the subsequent confirmed blocks are discarded.
With the robust and powerful protocols of blockchain security, a necessary solution can be implemented to decelerate the effects of the 51% attack. This is possible when the miners may divide the blockchain into two parts so that the one prone to maximum damage from the attack may now become meaningless.
This is because that part can’t deteriorate other miners working with the existing peers of the blockchain network. Henceforth, the damage from the attack is minimized now. Gradually, it will decrease if the network keeps on growing and begins to introduce more positive peers.
Furthermore, the reasons for obtaining reversed or altered transactions at high costs (with more confirmations) in the existing blockchain network are the same as those of growing blocks discussed in the above lines.
Another important point left as a solution is the acceptance of mining hardware. They are solely capable of offering high utilization of hardware resources with better GPU processing capability for efficient blockchain security.
Also, they can be customized and optimized extensively so that miners need not think about poor performance and poor GPUs while working on any of the networks (bitcoin) they are connected with.
Hence a successful attack will only be able to modify the transactions of a few recent blocks for a short period of time and even if a malicious entity is not motivated by profits and manages the successfully performed 51 (%) attack the blockchain protocol will be quickly adopted as a response.
-
Introducing multisig parameter for bitcoin users
We can take bitcoin as cash. If I have a hundred bitcoin stored on a bitcoin address, the same (address) will be having a corresponding private key.
This private key – if I can use – will help me spend these 100 bitcoin currency stores. But the limitation is that all these hundred dollars are tailored with numbers that combine together to make that bitcoin address.

If I lose that string of numbers or either it is stolen by hackers, all the money associated with my bitcoin account is gone.
Besides, the person to whom I told that address – if misuses the same – can also contribute to such a hack. How can one increase the existing blockchain security over this bitcoin account?
To help the bitcoin users, a multi-sig parameter is introduced for them. Now to withdraw money users need to insert more than one signature to go ahead with the transaction in a non-malicious manner.
With this multisig parameter, bitcoin users can now keep a wider control over the amount as none of the keys have custody or joint custody over the account(s).
Moreover, this parameter requires every hash value (bitcoin address) to acquire a pair of keys – one is public and the other one is private. This is because the locked and unlocked scripts associated with the wallet address can accept these signatures in a convenient and secure manner.
If one links the principle of multisig with blockchain security, it can be merely observed that every node has two keys. In case a node loses the information publicly, the loss can be recovered as the data is stored in the locked script that can only be accessed with the private key the particular node acquires.
Therefore, configuring the bitcoin wallet with customized settings has become much more reliable with the multisig parameter.
Moreover, bitcoin is working closely on improving the specifications of this parameter. Such improvements may include biometric access for the existing bitcoin wallets, two or multi-factor authentication when customized as per the users’ requirements, and so on.
To prevent online attacks, one may also choose the option of offline bitcoin – physical or paper. Similarly, there are other approaches bitcoin companies are planning to implement so that the risks that primarily happen with online transactions can be minimized to a greater extent. One such wallet – Trezor which uses multisig concept.

Those possessing a large number of bitcoins onto their accounts may use this wallet. When a bitcoin user opts for it, he/she will get a USB cable and a tamper-like storage unit. The user must configure the same by going to the official website of Trezor.
Then, he/she needs to enter the necessary information and later on, it will be mandatory to create a PIN. Such a secure way of identification will be helpful as no one can trace the bitcoin address onto which your money is stored.
Indistinguishably, it becomes imperative to synchronize the hardware unit with the Trezor account as all the transactions will only be successful after the effective communication of the storage unit and Trezor server.
But the fact that bitcoin users need to remember is that during the transaction, there should not be loss of internet connectivity. Plus the USB cord connecting the hardware unit and desktop/laptop (onto which Trezor account is running) must be in a working state.
Apart from all this, it is necessary to keep the hardware unit safe and you need to learn the process of setting up the Trezor accounts and customizing it in a much user-friendly manner. Notwithstanding, there might be the need for updates bitcoin asks for the downloading purpose.
You must follow the instructions carefully regarding the updates and install them as per the necessary blockchain security standards.
Although the user-agreement policies of this hardware unit are difficult to understand yet you must read them thoroughly so that any losses or cyber-attacks that may steal all the bitcoins from your account can be prohibited in a timely manner.
Can I solve my real-time problems with blockchain security?
The demand for blockchain and the currencies using its framework has increased after the hacking cases happened at Mt-Gox and other agencies offering crypto-currency exchange.
The maximum loss was 470 million US dollars in February 2014. Later, they were reported. Since then blockchain security and its associated protocols were made so powerful that they can flexibly be able to put a halt to such online hacks.
Furthermore, the 51 percent attack (its solutions), bitcoin multisig parameter, and the hardware unit – Trezor has cleared the doubts of many professionals regarding the ability of blockchain and its associated applications (cryptocurrencies) in solving real-time problems like failed online transactions, cyber attacks and so on.
Therefore, it is clear from the aforementioned solutions that the security standards of blockchain can stop the intruders anytime and let the developers create or break the existing blockchain network for making the virtual currency exchange system successful and trustworthy.
Such a system will be easy to accept and consists of features that invite an authentication mode so that if a person somehow loses the information, he/she can recover it within a lesser time.




